Psiphon
About Psiphon
Internet access isn’t equal across the world. In some countries, the internet most users experience is the open, more-or-less-uncensored network that hosts the websites and services you might expect. In others, government-imposed restrictions block major social media platforms, news sources, messaging apps, and various other services that ordinary users in less restricted countries take for granted.
Psiphon exists specifically for the second category, providing a censorship circumvention tool that helps users in restricted regions access the broader internet that political or technical barriers would otherwise hide from them.
This software has been around since 2006 and has accumulated a substantial user base concentrated heavily in countries with strict internet controls. Iran represents the largest single market, with Myanmar, Turkey, India, and Australia (where it’s often used to bypass workplace or school restrictions rather than government censorship) also showing strong adoption.
For journalists working under restrictive regimes, activists organizing in countries that target political speech, or ordinary users simply trying to read uncensored news, the tool has become something of a digital lifeline.
Censorship circumvention as the primary purpose
The defining feature of Psiphon is its focus on circumvention rather than privacy. Most users approach VPN-style tools thinking primarily about hiding their activity from their ISP, employer, or various surveillance entities. This software’s design optimizes for a different goal: getting your traffic past censorship infrastructure to reach destinations that censors are actively trying to block.
The distinction matters because the technical approaches differ. A privacy-focused tool prioritizes encryption, no-logging policies, and obscuring your activity from observers. A circumvention tool prioritizes evading detection by deep packet inspection systems, rapidly switching strategies when one approach gets blocked, and maintaining connectivity even when censors are actively trying to stop the tool from working.
This software handles the circumvention task by combining VPN, SSH, and SSH+ protocols, automatically selecting whichever currently works in your specific network environment. When censors successfully block one approach, the application falls back to alternatives, providing resilience that single-protocol tools lack.
The result is connectivity that often persists in environments where other circumvention tools have been completely blocked.
Multiple protocols and automatic selection
The protocol diversity is genuinely important to how the tool functions. Direct VPN connections work in many networks but get blocked in countries where authorities specifically target VPN traffic. SSH-based connections look different on the network, sometimes evading detection where VPN signatures would be flagged. SSH+ adds an additional obfuscation layer that disguises traffic to look like ordinary HTTPS browsing, evading detection methods that successfully identify regular SSH.
When you start the application, it automatically tests which protocols work in your current network environment, selecting whichever provides the best combination of working connectivity and acceptable performance. If your initial protocol gets blocked during a session, the application transparently switches to alternatives without interrupting your active connections meaningfully.
For example, if a government firewall detects and blocks common VPN connections, the tool falls back to SSH+ mode, making the traffic look like regular secure web browsing. This kind of constant adaptation keeps the door open even in environments with the most sophisticated filtering systems, where simpler tools fail completely.
Server selection and advanced configuration
While the automatic mode works well for most users, the application also allows manual server selection from a list of available regions. Choosing servers closer to your country typically produces better speeds, and experimenting with different servers when one connection feels slow often resolves performance issues. For most users, the default automatic selection works flawlessly, but having manual control available matters for users who want to optimize specific scenarios.
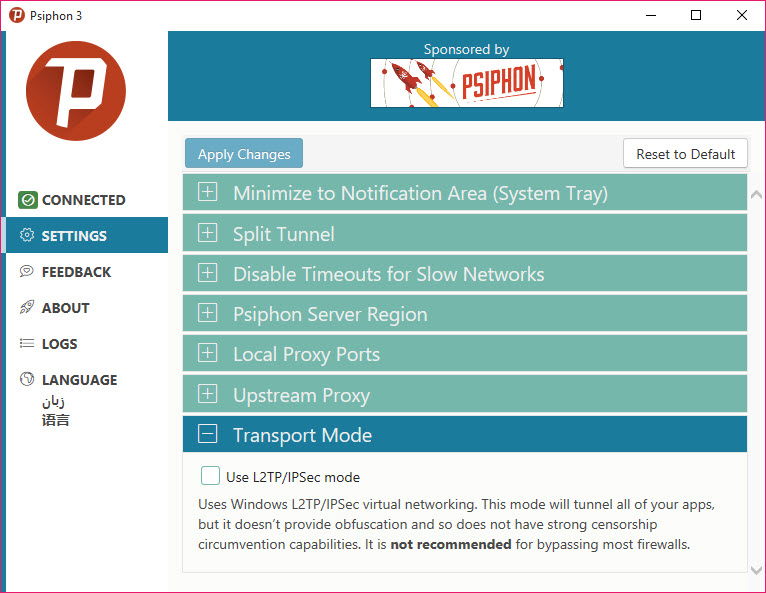
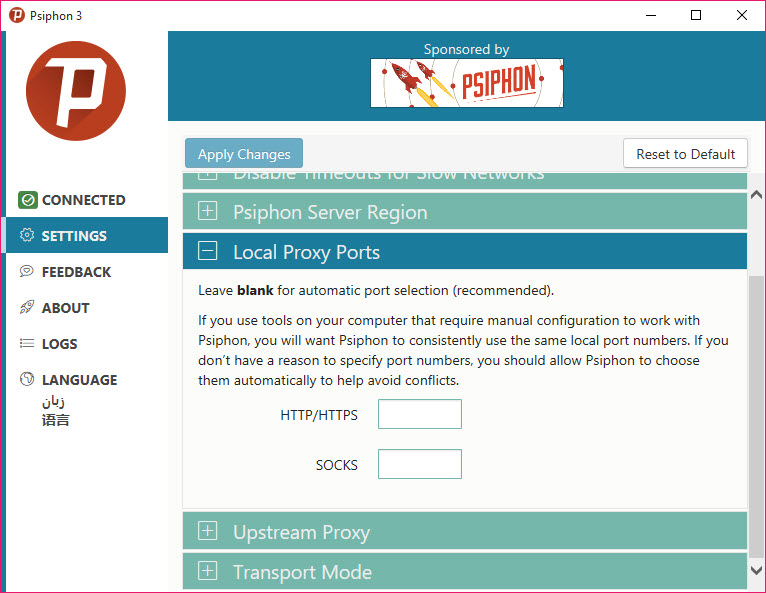
Beyond server choice, advanced settings let you change the port number, tweak protocol preferences, and adjust various other technical parameters. These options are buried in advanced menus rather than the main interface, which keeps the basic experience simple while still providing depth for users who want to fine-tune behavior.
Most users will never need these settings; the few who do appreciate them being available.
Free version with optional Speed Boost
The base version of Psiphon is genuinely free and provides full circumvention functionality without artificial restrictions. Users can connect, browse, and access blocked content without payment in any way. The free version caps speeds at around 2 Mbps, which handles browsing, messaging, and reading blocked news sites comfortably but isn’t sufficient for high-definition streaming or large downloads.
The Speed Boost feature, powered by PsiCash tokens, removes these speed caps for periods of time. PsiCash tokens can be earned through various in-app activities or purchased directly, with the time-limited boost approach letting users get faster speeds when they specifically need them rather than committing to ongoing subscription payments.
The dual-tier model has been carefully designed to ensure the free tier remains functional for users who actually need the tool for circumvention purposes.
Unlike some “freemium” services that cripple the free version to push users toward payment, the basic functionality here remains genuinely useful for the political users the tool was designed to serve.
Real-world resilience during internet shutdowns
A particularly compelling demonstration of Psiphon capabilities has come during major internet shutdowns when governments have moved aggressively to cut their populations off from the outside world. During shutdowns in Cuba and Myanmar, usage numbers skyrocketed as millions of users turned to the tool when other circumvention methods failed. Iran has similarly seen massive usage spikes during political crackdowns when authorities have throttled or blocked the broader internet.
This resilience under adversarial conditions is what genuinely sets the tool apart. Anyone can build a VPN that works when authorities aren’t trying to block it. Building a service that maintains functionality when sophisticated state actors are actively working to defeat it requires fundamentally different engineering, with the multi-protocol approach and continuous adaptation to censorship developments producing connectivity that simpler tools simply can’t match.
For users in stable democracies who only encounter circumvention tools occasionally, this resilience is invisible. For users in countries where access to information is treated as a political battleground, it’s the entire reason the tool exists.
The Conduit feature for sharing bandwidth
A particularly interesting feature is Psiphon Conduit, which lets users in unrestricted regions share their bandwidth to help users in restricted regions reach the open internet. Running Conduit on your computer turns it into a small relay that connects users in censored countries to the destinations they want to reach.
For users who want to support digital freedom causes, this provides a concrete way to contribute infrastructure rather than just supporting through donations. The bandwidth sharing happens with controls letting you specify how much of your connection to dedicate, when to be active, and various other parameters that prevent the relay activity from interfering with your own internet usage.
The Conduit approach is genuinely useful infrastructure for the project, since growing the network of relay nodes makes the service more resilient against censorship efforts. Each additional Conduit user provides another path that censors have to identify and block, with the increasing diversity making complete blocking increasingly impractical.
Privacy considerations and what the tool isn’t
A common misconception about Psiphon is that it provides the same level of privacy protection as a commercial VPN service. The honest assessment is more nuanced. The tool encrypts your connection between your device and the Psiphon network, which protects your traffic from local network observers like your ISP, your employer’s network monitoring, or anyone snooping on the wifi network you’re using.
Beyond that point, the tool’s focus on circumvention rather than privacy means certain protections that privacy-focused VPNs offer aren’t part of this tool’s design. There’s no kill switch to prevent traffic leaks if the connection drops, no DNS leak protection in the way commercial VPNs implement it, and some metadata such as IP addresses and connection timestamps may still be logged. Security experts generally recommend the tool for unblocking content rather than for highly sensitive activities where complete anonymity is required.
For users in restrictive countries primarily concerned with accessing blocked content, the privacy provided is sufficient for most realistic scenarios. For users who specifically need protection against well-resourced surveillance entities, additional tools like Tor should supplement this software’s circumvention capabilities rather than relying on it alone.
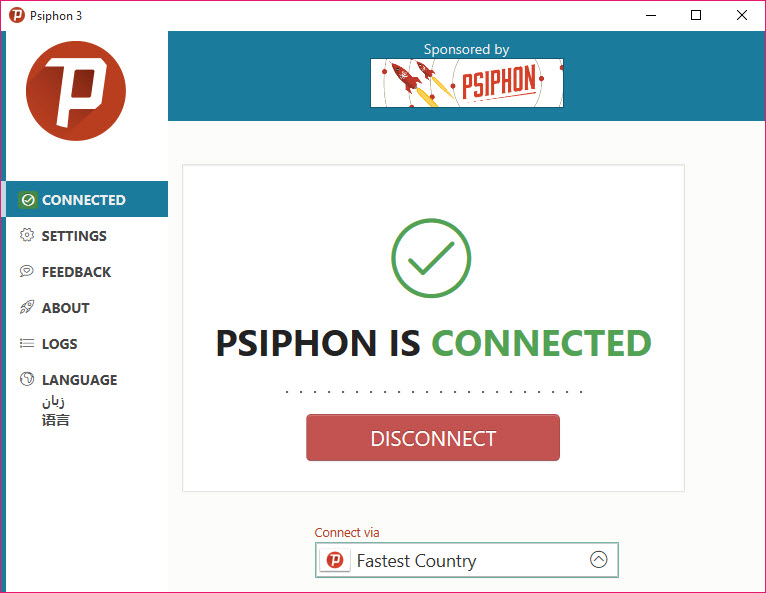
Beginner-friendly interface with depth available
The graphical interface is straightforward, with a prominent Connect button and a server selection option as the only choices most users will ever need to engage with. Click Connect, wait a few seconds for the protocol selection and connection establishment, and you’re ready to browse blocked content. The whole experience is accessible to users with no technical background.
For users wanting more control, the advanced menus provide access to protocol preferences, port configuration, and various other technical parameters. These options stay out of the way during normal use but are available when needed, providing depth without complicating the basic experience.
Multilingual support makes the tool accessible to users worldwide regardless of their language, which matters substantially for a tool whose core users are spread across countries where English isn’t the primary language. The interface translations cover the major languages spoken in the regions where the tool sees heaviest use.
The “is it safe” question and trust considerations
Common search queries involve whether Psiphon is safe to use. The technical answer is that the application itself isn’t malware and downloads from official sources are legitimate. The development team has academic origins through the Citizen Lab project, with continued development by people whose stated mission is supporting digital freedom rather than commercial extraction or surveillance.
The trust considerations are different from typical software. By using the tool, you’re routing your internet traffic through infrastructure operated by Psiphon Inc., which means trusting them with what you do during sessions. The company’s stated policies and academic origins suggest legitimate intentions, but users should understand that any circumvention tool requires some trust in whoever operates the infrastructure.
The other safety consideration involves legal exposure in countries where using circumvention tools is itself illegal. Users in those jurisdictions face risks not from the tool but from local authorities discovering they’re using it, with the practical implications varying enormously by country. The tool provides circumvention capability; managing the legal context of that circumvention remains the user’s responsibility.
Considerations and limitations
The tool’s effectiveness varies by country and over time as the cat-and-mouse game between circumvention tools and censorship infrastructure evolves. What works perfectly today might be partially blocked tomorrow if censors successfully identify and target current protocols. The development team continuously updates the application to maintain effectiveness, but periods of reduced functionality occasionally occur after major censorship escalations.
Some specific countries with the most aggressive internet censorship, particularly China with its comprehensive Great Firewall, present significant challenges that this software handles less reliably than smaller circumvention efforts. For Chinese users specifically, results vary substantially and other tools may serve better depending on current conditions.
The 2 Mbps cap in the free version, while sufficient for browsing and reading text-based content, becomes limiting for users who want to stream video or download larger files regularly. The Speed Boost option addresses this for users willing to engage with the PsiCash token system, but users expecting unlimited free high-speed access will be disappointed.
Conclusion
Psiphon has earned its position as one of the most respected censorship circumvention tools by genuinely delivering what its mission promises. The combination of multiple protocols, automatic adaptation to network conditions, free availability for users who need it most, and academic origins focused on digital freedom rather than commercial extraction produces a tool that serves a specific and important purpose better than commercial alternatives.
It’s not the right choice for every use case. Users primarily concerned with privacy rather than circumvention are better served by purpose-built privacy tools, and users wanting maximum streaming speeds will find consumer VPN services more polished for that specific purpose.
But for the substantial audience of users in countries with internet censorship, journalists working in restrictive environments, or anyone who needs to access blocked content as a matter of necessity rather than convenience, Psiphon delivers exactly that, with the kind of mission-focused capability that has kept it relevant across nearly two decades of evolving global censorship dynamics.
Pros & Cons
- Multiple protocol support automatically selects whichever currently works
- Free tier provides genuinely functional circumvention without artificial restrictions
- Open-source codebase allows independent verification of what the software does
- Academic origins through Citizen Lab provide legitimacy beyond commercial VPN services
- Manual server selection and advanced configuration available for users wanting control
- Conduit feature lets users in free countries support those in censored regions
- Designed specifically for adversarial environments where censors actively target tools
- Proven resilience during major internet shutdowns in Cuba, Myanmar, and elsewhere
- Multilingual support accessible to users worldwide
- Free version capped at around 2 Mbps, insufficient for video streaming or large downloads
- Lacks advanced VPN features like kill switch and DNS leak protection
- Privacy protections less comprehensive than purpose-built privacy tools
- Some heavily censored countries (notably China) present persistent challenges
- Performance varies based on current network conditions and server load
- Legal exposure in countries where circumvention itself is illegal remains user responsibility
Frequently asked questions
This software is a censorship circumvention tool that helps users bypass internet restrictions imposed by governments, employers, schools, or other entities controlling network access. It combines VPN, SSH, and SSH+ protocols, automatically selecting whichever currently works in your specific network environment to provide connectivity to blocked websites and services.
The application includes VPN functionality but is more accurately described as a circumvention tool. It uses VPN protocols among several other approaches, automatically switching between them based on what works in your environment. Where commercial VPNs prioritize privacy and geo-unblocking, this tool prioritizes maintaining connectivity in environments where censors are actively trying to block circumvention.
The application itself is safe and legitimate, with academic origins through the Citizen Lab at the University of Toronto and continued development by people whose stated mission is supporting digital freedom. The trust required is similar to any circumvention tool: you're routing traffic through infrastructure operated by the development team. The open-source nature allows independent verification of what the software does.
Effectiveness in China specifically varies and tends to be less reliable than in countries with less sophisticated censorship infrastructure. The Great Firewall presents particular challenges that often defeat circumvention tools, with results depending on current conditions and ongoing arms-race dynamics. Users in China may need to try multiple tools to find what currently works.
Yes, the application includes a manual server selection option that lets you choose specific server regions rather than letting the tool select automatically. Choosing servers closer to your country typically produces better speeds, and switching servers when one connection feels slow often resolves performance issues. The automatic mode works well for most users, but the manual option remains available for those who want it.
Free users will find the 2 Mbps speed cap limiting for high-definition video streaming or large downloads, though it handles text-based browsing, messaging, and standard-definition video adequately. The Speed Boost feature can temporarily improve performance for these scenarios, but the tool generally remains slower than dedicated commercial VPNs by design, since its priority is circumvention rather than maximum throughput.
Conduit lets users in countries without internet censorship share their bandwidth to help users in restricted countries access the open internet. Running it turns your computer into a small relay that supports the network. The configuration includes controls for how much bandwidth to share and when to be active, allowing supportive participation without disrupting your own internet usage.

 (472 votes, average: 4.14 out of 5)
(472 votes, average: 4.14 out of 5)