ProtonVPN
About ProtonVPN
ProtonVPN is the VPN service from Proton AG, the Swiss company started in 2014 by scientists from CERN and MIT who originally built ProtonMail to address email privacy after the Snowden disclosures. The VPN launched in 2017 as part of the broader Proton ecosystem, with the same engineering team and the same emphasis on demonstrable privacy through technical implementation rather than marketing claims.
The headline feature for users new to the category is the genuinely free tier with no data caps, no advertising, and no time limits on usage. Free accounts get servers in five countries with reasonable speeds, while paid Plus and Unlimited plans expand to over 14,000 servers across 110+ countries with additional capabilities like Secure Core multi-hop routing, Tor integration, NetShield ad blocking, and access to streaming services.
The technical foundation differs from typical commercial VPNs in ways that matter for users who actually evaluate VPN security. The applications are open source on GitHub, which means independent security researchers can verify the code matches the company’s claims rather than trusting marketing. T
he no-logs policy has been audited by external firms with reports published. Swiss jurisdiction provides legal protections that US-based and UK-based VPNs can’t match because of differences in surveillance laws and data retention requirements between countries. The infrastructure supports WireGuard alongside OpenVPN and the company’s Stealth protocol designed for restrictive networks where standard VPN traffic gets blocked.
Active development continues with regular updates that add features and improve performance, with the company having grown substantially while maintaining the privacy-focused positioning that distinguishes it from typical commercial VPN providers focused primarily on consumer marketing.
Swiss jurisdiction and what it actually means
The Swiss legal framework matters substantially for VPN services because privacy protection depends on what governments can compel companies to do, not just what companies promise. Switzerland is not part of the Five Eyes, Nine Eyes, or Fourteen Eyes intelligence-sharing agreements that the US, UK, Canada, Australia, New Zealand, and various European countries participate in. Swiss privacy laws include Article 13 of the Federal Constitution that explicitly protects privacy and data protection, with the Federal Act on Data Protection providing detailed protections for personal information.
The practical implication is that Swiss courts can’t compel Proton AG to log user activity that wasn’t being logged. Foreign governments requesting user data through Mutual Legal Assistance Treaties have to work through Swiss courts that apply Swiss privacy standards. Various legal mechanisms that produce data turnover from US-based or UK-based services don’t apply to Swiss companies in the same way.
The jurisdiction doesn’t make Swiss services immune to all legal process. Swiss authorities can compel data turnover through proper legal channels for criminal investigations. The protection is about which legal regime applies and what that regime requires rather than about complete legal immunity. For users evaluating VPN providers, the difference between Swiss jurisdiction and Five Eyes jurisdictions produces meaningfully different privacy outcomes for similar threat models.
For users specifically focused on legal jurisdiction as their primary VPN selection criterion, this jurisdictional foundation is genuinely uncommon among major VPN providers. Most major commercial VPNs are based in the US, UK, or various Caribbean and Pacific tax havens. The Swiss positioning here matches what sophisticated privacy users actually evaluate when comparing services rather than simply trusting marketing claims.
The free tier without data caps
The free tier is genuinely free in ways that other “free VPN” offerings typically aren’t. Most free VPN services impose data caps (typically 500 MB to 10 GB per month), session limits, time restrictions, or various other constraints designed to push users toward paid tiers. This service provides unlimited data on the free tier, with no monthly caps, no daily limits, and no time restrictions on usage.
The free tier covers the actual use case of “I need a VPN sometimes for basic privacy and circumvention” without forcing users to pay for capabilities they may not need. Servers are limited to five countries (the US, Netherlands, Japan, Romania, and Poland depending on current configuration), which restricts geographic flexibility but doesn’t constrain how much you can actually use the service. Speeds on free servers are typically lower than paid servers because free users share fewer servers, but the speeds remain adequate for browsing, email, and various other normal activities.
The economics of the free tier work because the company subsidizes free users through paid subscribers. Premium subscribers pay for the broader server network, additional features, and various other capabilities, with the free tier serving both as an entry point into the ecosystem and as a public commitment to privacy availability regardless of payment. The model differs from advertising-supported free VPNs that monetize free users through advertising or data collection, with this service explicitly avoiding both.
For users wanting basic VPN protection without subscription commitment, the free tier handles their needs. For users wanting full server selection, multi-hop routing, streaming access, and various other premium features, the paid tiers cover those scenarios.
The clear separation between tiers prevents the bait-and-switch experiences common with free services that turn out to require payment for actual usefulness.
Open source applications and verifiable privacy
The Windows, macOS, Linux, Android, and iOS applications are all open source with code available on GitHub. The transparency matters because privacy claims become verifiable rather than requiring trust in company assertions. Independent security researchers regularly audit the code, with findings published rather than kept internal. The applications have been audited by SEC Consult and Securitum among others, with audit reports available publicly.
The open source approach contrasts with most commercial VPN providers whose closed-source applications can only be evaluated through reverse engineering or behavioral analysis. Users specifically concerned about VPN application behavior have meaningful ability to evaluate this service that competitors don’t enable. The verification capability matters most for users in the privacy-focused subset who actually evaluate technical claims rather than just reading marketing.
The transparency extends to the no-logs policy through external audits. The company publishes audit reports from external firms confirming that the technical implementation actually matches the no-logs claim. The audits cover both the application behavior and the server infrastructure, with the result being privacy claims that survive independent verification rather than relying purely on company assertions.
For users wanting to verify specific behaviors themselves, building the applications from source is straightforward through standard development tools. The build process is documented in the repository’s README files. Comparing the built result with the binaries the company distributes confirms that the binaries match the source code rather than containing hidden functionality. This verification capability is genuinely uncommon among commercial VPN providers.
Secure Core and multi-hop routing
Secure Core is the multi-hop feature available on paid tiers that routes traffic through two VPN servers in different countries before reaching the destination. The first hop happens in privacy-friendly jurisdictions including Switzerland, Iceland, and Sweden, with the second hop being whichever exit country the user selects. The architecture provides protection against attacks that monitor exit servers because the exit server only sees traffic coming from the secure core entry rather than from the user’s actual IP address.
The use case for Secure Core involves threat models where the exit server might be compromised or monitored. Standard single-hop VPN routing means a compromised exit server can see users’ real IP addresses (the previous hop). Secure Core routing means a compromised exit server sees only the secure core entry server’s IP, with the actual user IP being one additional hop further away. The protection isn’t free because additional hops add latency and reduce throughput, but for users with specific threat models that justify the trade-offs, the capability matters.
The privacy-friendly entry country selection is deliberate. Switzerland (where the company is based), Iceland (with strong privacy laws and physical security), and Sweden (with cooperative legal framework for the entry servers’ physical location) all provide legal protections that other countries don’t match. The architecture treats these jurisdictions as the trusted entry points, with exits anywhere being protected by the entry point’s location.
For users wanting Tor-style anonymity properties beyond what single-hop VPNs provide, Secure Core fits some scenarios while Tor-based tools fit others. The choice depends on whether you primarily need exit-side protection (where multi-hop VPN works) or entry-side protection (where Tor’s three-hop random routing produces stronger anonymity properties).
Protocol support including WireGuard
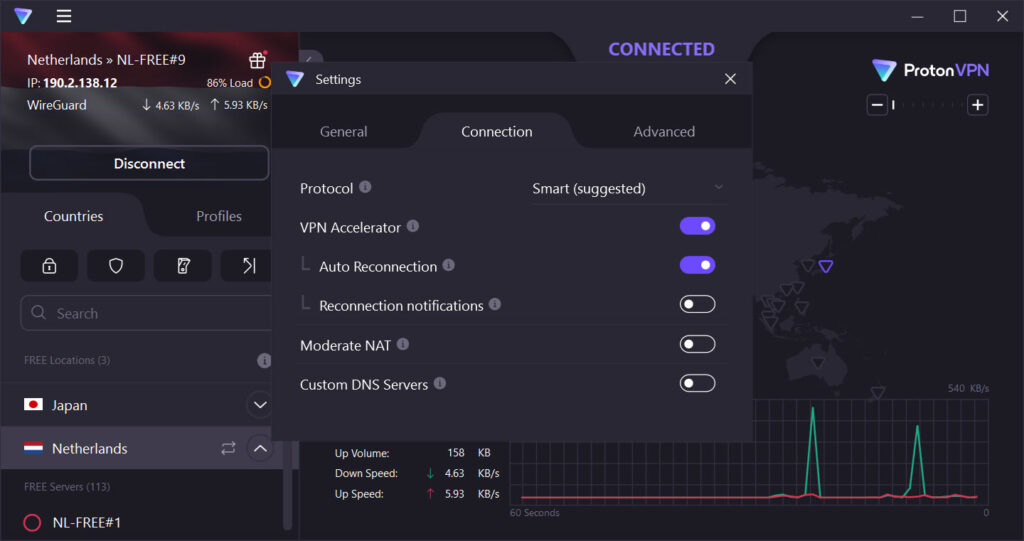
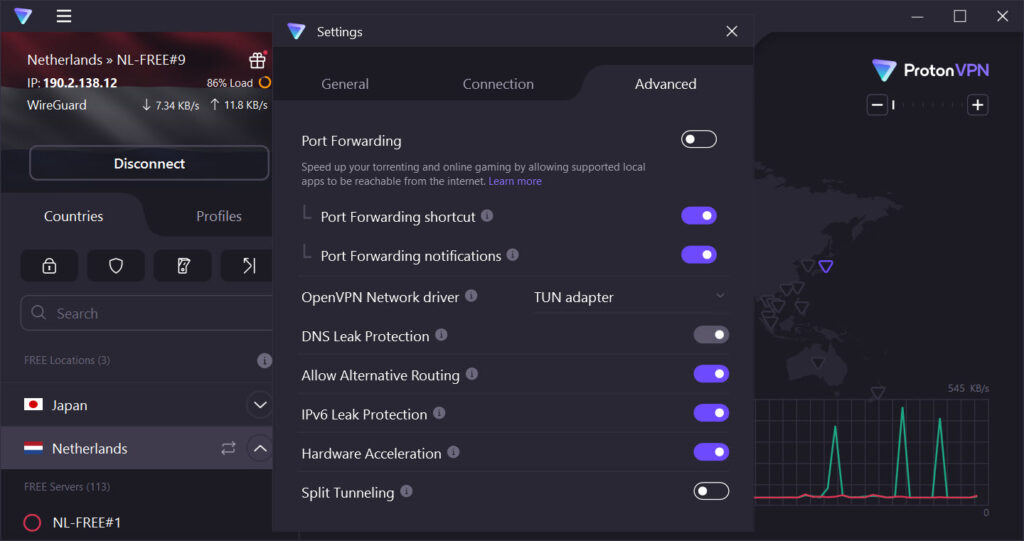
The service supports OpenVPN, IKEv2, and WireGuard alongside the company’s Stealth protocol designed for restrictive networks. WireGuard is the modern protocol that’s substantially faster and more efficient than OpenVPN for typical scenarios, with the implementation here being the standard WireGuard rather than a proprietary fork. For users who want maximum speed, WireGuard is typically the right choice, with OpenVPN being available for compatibility with networks or scenarios where WireGuard doesn’t work as well.
The Stealth protocol handles the case where standard VPN protocols get blocked. Networks that use deep packet inspection to identify and block VPN traffic can detect OpenVPN, WireGuard, and various other standard protocols by their packet signatures. Stealth wraps the VPN traffic in TLS that looks like normal HTTPS traffic, which makes it substantially harder to identify and block through traffic analysis. Users in restrictive networks (China, Iran, various other countries with active VPN blocking) benefit from Stealth in ways that standard protocols can’t deliver.
The protocol availability differs across platforms based on operating system support. Some protocols work better on specific platforms due to operating system networking implementations. The application typically chooses appropriate defaults for each platform while letting users override the choice for specific scenarios where they want different protocols. For users comfortable with OpenVPN configuration directly through standalone clients, configuration files for self-managed connections are also available.
The protocol switching happens through the application interface without requiring separate connection management. Switch between WireGuard for daily use, Stealth when you encounter blocking, and OpenVPN for specific compatibility scenarios, all through the same application.
The flexibility matches what real-world VPN usage actually involves rather than locking users into a single protocol regardless of changing network conditions.
Tor over VPN integration
The Tor over VPN feature routes traffic through the Tor network after exiting the VPN, providing combined VPN privacy and Tor anonymity through one connection. Connect to a Tor-enabled server, and your traffic exits the VPN through a Tor entry node, traverses the Tor network through three hops, and reaches your destination from a Tor exit node. The combination provides stronger anonymity properties than either VPN or Tor alone produce.
The architecture matters for specific threat models. Tor alone has the issue that ISPs can see you’re using Tor (the first connection from your computer to a Tor entry node is identifiable as Tor traffic). VPN alone has the issue that the VPN provider sees your real IP address even though websites don’t. Combining them addresses both concerns. The VPN sees your real IP but only that you’re using VPN. The Tor network sees Tor traffic but not your real IP. The destination sees Tor exit node traffic without any direct connection to either your IP or the VPN.
The performance cost is genuinely substantial. Tor itself produces substantial latency and bandwidth limitations. Adding VPN encryption on top compounds these limitations. The combination is appropriate for scenarios where anonymity matters substantially more than performance rather than for general browsing where the speed cost would be unacceptable.
For users wanting Tor capability without VPN integration, dedicated Tor browsers handle the use case directly. The integrated approach here fits scenarios where you specifically want both VPN routing (with the protection that provides) and Tor anonymity (with the additional protection that adds). For most users, single-hop VPN through this service handles the threat models they actually face, with Tor over VPN being available for the specific scenarios that justify the performance cost.
NetShield ad and malware blocking
NetShield is the DNS-based filtering feature that blocks ads, trackers, and known malware domains at the VPN level. The implementation works by maintaining blocklists of advertising and tracking domains, then refusing to resolve those domains when DNS queries flow through the VPN. The user-visible effect is that ads don’t load on websites, trackers can’t reach their reporting servers, and malware sites don’t resolve at all if you accidentally click links to them.
The DNS-level approach catches advertising and tracking before HTTP connections start, which produces faster page loads compared to browser-based ad blockers that download ad content before blocking display. Pages with substantial advertising load measurably faster through NetShield than through direct connections without ad blocking. The bandwidth savings compound across heavy browsing sessions.
The malware blocking adds a layer of protection that’s distinct from antivirus software. Where antivirus catches malicious files after they reach your computer, NetShield prevents connections to known malicious sites in the first place. The protection is automatic without requiring user awareness of which sites might be problematic, which fits how phishing and malware distribution actually work in practice.
NetShield availability differs between free and paid tiers. The basic ad and malware blocking is available on free accounts, with full tracker blocking and various other categories being part of paid subscriptions. For users primarily wanting ad blocking, the free tier covers their needs. For comprehensive tracker blocking and various other privacy enhancements, paid tiers add additional categories.
Working in restrictive networks
The service works in countries with active VPN blocking better than most competitors do. China specifically blocks essentially all standard VPN traffic, with the Great Firewall using deep packet inspection plus active probing to identify and block VPN connections. Most commercial VPNs become unreliable or completely non-functional in China during periods of intensive blocking. This service maintains functionality through the Stealth protocol’s traffic obfuscation combined with infrastructure changes that respond to blocking attempts.
The reliability isn’t perfect. Periods of intensive blocking by Chinese authorities sometimes affect this service alongside competitors. The difference is that the company actively works to maintain functionality through these periods rather than simply giving up on Chinese users. Users in China who specifically need VPN access find this service producing better results than most alternatives during ongoing usage rather than just during quiet periods.
Other restrictive networks (Iran, various Middle Eastern countries, certain corporate networks) similarly block standard VPN protocols with varying degrees of intensity. The Stealth protocol handles most of these scenarios, with the implementation specifically designed to look like normal TLS traffic to network filters. The protocol works because TLS is essential to modern web browsing, with networks unable to block TLS without also breaking normal internet usage.
For users in restricted regions evaluating VPN options, the practical effectiveness in their specific network matters substantially more than abstract feature lists. Free tier access lets users in these regions test the service before committing to subscriptions, with the testing covering whether the service actually works in their specific environment rather than relying on general claims about restrictive network support.
Considerations and limitations
The free tier server selection is genuinely limited compared to paid tiers. Free users get servers in only a few countries, with the limitation affecting both geographic flexibility for content access and connection options when specific countries are needed. Users who specifically need servers in countries beyond the free tier’s selection require paid subscriptions.
Streaming service compatibility varies. Premium tiers include Plus servers specifically optimized for accessing streaming services that block VPN connections, with the result being reasonable Netflix, Hulu, BBC iPlayer, and various other streaming service access. Free tier servers don’t get this optimization, which means streaming through the free tier produces inconsistent results. For users primarily wanting VPN for streaming, paid tiers become functionally necessary.
The connection speeds on heavily-loaded free servers can be substantially slower than paid servers. Free servers see disproportionately heavy usage relative to their capacity because all free users share them, with the result being that peak times produce noticeably slower performance. Paid users get access to substantially more servers across more locations, which distributes the load and produces more consistent performance.
Some specific applications and protocols don’t work well over VPN regardless of which provider you use. Voice and video calling sometimes produces quality issues through any VPN due to latency. Online gaming often produces noticeable lag through VPN connections. Various other latency-sensitive applications experience similar issues. Users with specific use cases requiring minimum latency should test the service for their specific scenarios rather than expecting transparent VPN coverage of all internet activity.
The price point for paid tiers is competitive but not the cheapest option in the market. Various commercial VPNs offer lower prices, particularly with multi-year commitments. Users prioritizing minimum cost find cheaper alternatives, with the trade-off being whether the privacy and technical foundations matter enough to justify the price difference. Compared to alternatives like NordVPN at similar price points, the differentiators are more about jurisdiction, open source status, and specific features than price.
Conclusion
For users who actually evaluate VPN services based on technical privacy fundamentals rather than just marketing or price, ProtonVPN delivers a service that survives the deeper scrutiny that most commercial VPNs avoid. Swiss jurisdiction matters because legal frameworks affect what privacy protection is actually possible. Open source applications matter because verifying privacy claims requires being able to inspect what the software actually does.
External audits matter because they convert privacy promises from marketing into independently-confirmed technical facts. The free tier without data caps matters because it lets users with basic privacy needs access protection without paying, while paid tiers provide the broader server network and additional capabilities that more demanding users actually need.
The application fits users who want their VPN choice to reflect demonstrable privacy fundamentals rather than just feature checklists or aggressive pricing. The free tier covers limited countries, paid tiers aren’t the cheapest options available, and some advanced features remain locked behind premium subscriptions.
For users whose threat model involves wanting credible privacy protection through technically verifiable means, the foundations here justify the choice over alternatives that depend on trusting marketing claims that competitors can’t actually verify.
The fact that the same company has maintained this position consistently since 2014 across an expanding ecosystem of privacy tools produces a track record that newer entrants in the privacy-focused VPN category haven’t accumulated.
Pros & Cons
- Genuinely free tier without data caps or time restrictions
- Swiss jurisdiction provides legal privacy protections that Five Eyes jurisdictions don't match
- Open source applications enable independent verification of privacy claims
- No-logs policy verified through external audits with published reports
- Secure Core multi-hop routing through privacy-friendly jurisdictions on paid tiers
- WireGuard, OpenVPN, IKEv2, and Stealth protocol support across platforms
- Tor over VPN integration combines VPN and Tor anonymity through one connection
- NetShield blocks ads, trackers, and malware at the DNS level
- Works in heavily-restricted networks including China through Stealth protocol
- Same company ecosystem as ProtonMail, Proton Drive, and Proton Calendar
- Free tier limited to servers in only a few countries
- Streaming service access requires paid Plus servers rather than free tier
- Free tier speeds vary substantially based on server load
- Premium subscriptions are competitive but not the cheapest VPN option available
- Some advanced features only available on Plus or Unlimited tiers
Frequently asked questions
This software is a VPN service from Proton AG, the Swiss company started in 2014 by scientists from CERN and MIT. The VPN launched in 2017 alongside ProtonMail and various other Proton privacy tools. It provides encrypted internet connections through over 14,000 servers in 110+ countries on paid tiers, with a genuinely free tier offering unlimited data on servers in five countries. The applications are open source, the no-logs policy is audited externally, and Swiss jurisdiction provides legal privacy protections that other jurisdictions don't match.
The application establishes encrypted connections from your device to one of the company's VPN servers, with all internet traffic routing through that encrypted tunnel. Websites and other internet services see traffic coming from the VPN server's IP address rather than your real IP. The encryption protects your traffic from being read by your internet service provider, network operators, or other parties between you and the VPN server. The service supports multiple protocols including WireGuard for speed, OpenVPN for compatibility, and Stealth for restrictive networks.
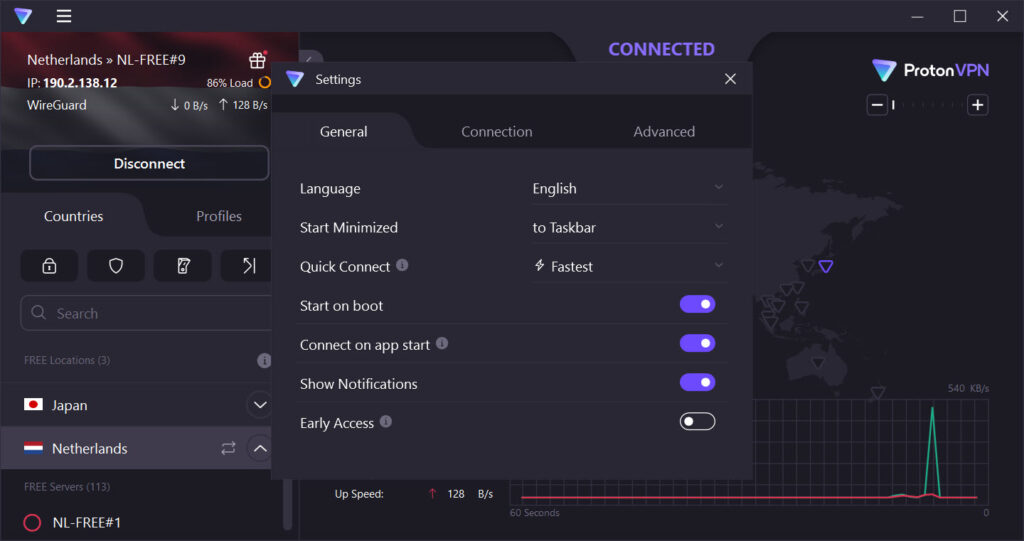
Install the application from the company's website or app store, sign in with your Proton account (free or paid), and click connect. The application chooses an appropriate server automatically, or you can select specific servers, countries, or specialized servers (Secure Core, Tor over VPN, streaming-optimized) through the interface. Connection establishment typically takes a few seconds, after which all internet traffic from your device routes through the VPN. Disconnect through the application interface when you want to return to direct connections.
Proton AG, a Swiss company founded in 2014 by Andy Yen, Jason Stockman, and Wei Sun. The founders met at CERN (the European Organization for Nuclear Research) where they were working on particle physics research. The company started with ProtonMail and expanded into the VPN service alongside other privacy-focused products including Proton Drive (encrypted cloud storage), Proton Calendar (encrypted calendar), and Proton Pass (password manager). The ownership has remained consistent since founding, with the company being structured as a Swiss-based privacy company.
The no-logs policy explicitly states that the service doesn't log user activity, with external audits confirming the technical implementation matches this claim. The auditors have access to server infrastructure and application code to verify that no logging happens. The policy and audit reports are published publicly. Swiss law doesn't require VPN services to log user data the way some other jurisdictions do, which means the no-logs claim is supported by both technical implementation and legal framework rather than just company policy.
Yes, the service maintains functionality in China better than most competitors. The Stealth protocol's traffic obfuscation makes connections appear similar to normal TLS web traffic, which substantially complicates attempts to block VPN connections through deep packet inspection. The reliability isn't perfect because Chinese authorities actively work to block VPN services, but functional periods are more reliable than what most commercial VPNs maintain. Users in China can test functionality through the free tier before committing to paid subscriptions.
The distinguishing features include Swiss jurisdiction (rather than US or UK), open source applications (rather than closed source), audited no-logs policy with published reports (rather than just policy claims), genuinely free tier without data caps (rather than free trials or restricted free tiers), Secure Core multi-hop routing through privacy-friendly countries, and integration with the broader Proton ecosystem of privacy tools. For users primarily evaluating VPNs based on privacy fundamentals rather than just price or feature lists, these differentiators matter more than they do for users with simpler requirements.
Secure Core is the multi-hop feature available on paid tiers that routes traffic through two VPN servers in different countries before reaching the destination. The first hop happens in privacy-friendly jurisdictions including Switzerland, Iceland, and Sweden. The second hop is whichever exit country you select. The architecture protects against attacks that monitor exit servers because the exit server only sees traffic from the secure core entry rather than from your real IP address. The performance cost is real (additional latency and reduced throughput), but the privacy benefit matters for specific threat models.
Service interruptions happen occasionally due to various causes including server maintenance, infrastructure changes, and active blocking attempts in restrictive networks. The company maintains a status page that reports current service health and any ongoing incidents. Most interruptions resolve within minutes to hours rather than producing extended outages. For users in restrictive networks where blocking happens periodically, switching protocols (especially to Stealth) often resolves connection issues that other protocols can't bypass.
For free accounts, simply stop using the service. There's nothing to cancel because no payment is involved. For paid subscriptions, log into your Proton account through the web interface, navigate to subscription settings, and choose the cancellation option. The cancellation takes effect at the end of your current billing period, with the account reverting to free tier status afterward. Refund policies for early cancellation depend on which subscription tier and how recently you subscribed, with the company's terms documenting specific conditions.

 (140 votes, average: 4.06 out of 5)
(140 votes, average: 4.06 out of 5)