Universal Virus Sniffer
About Universal Virus Sniffer
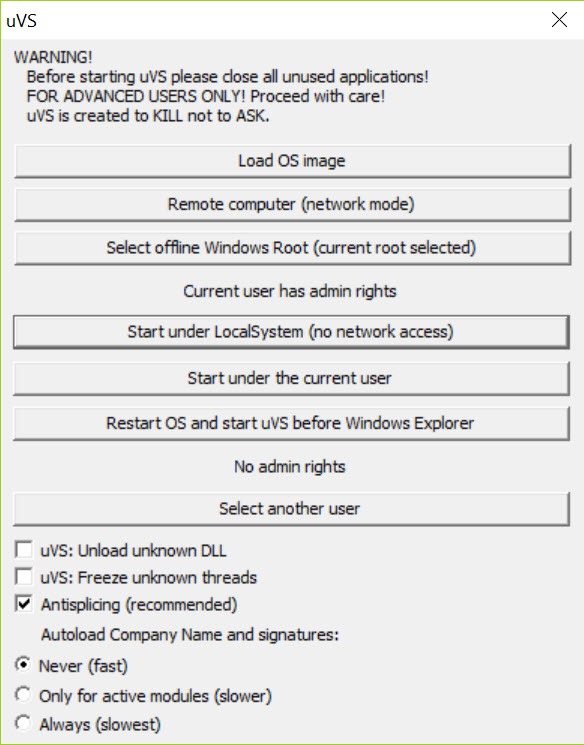
Universal Virus Sniffer (uVS) is a security tool built around a different premise than mainstream antivirus: instead of automatically scanning and removing threats based on a vendor’s threat database, it gives you the manual control to analyze a system, identify suspicious components yourself, and remove them through scripts you generate.
The application is designed for situations where conventional antivirus has either missed something, can’t remove what it found, or where you need to clean an infection so deeply embedded that automated tools refuse to touch it. The target audience is technically deliberate: tech support professionals, malware removal forum specialists, system administrators handling compromised machines, and advanced users who treat malware cleanup as a forensic exercise rather than a one-click operation.
The application runs as a single portable executable with no installation, no system service, and no permanent footprint. Launch it, scan the system, and you get a complete inventory of every active executable, every loaded driver, every autorun entry, every scheduled task, and every signed binary running on the machine. Each item shows its file path, digital signature status, hash, and various other forensic details that help distinguish legitimate components from suspicious ones.
The output isn’t a “clean/infected” verdict; it’s the raw evidence you use to make that verdict yourself, which is exactly the point for users who don’t trust automated decisions on systems where the cost of getting cleanup wrong is substantial.
Active virus signature extraction
The defining capability is automatic signature extraction from active malicious files. When the application detects a suspicious component during a scan, it can pull the byte signature of the file directly and add it to a local detection database. This matters because freshly-discovered malware (the kind that hasn’t yet shown up in commercial vendor databases) can be detected on subsequent scans of other systems once you’ve extracted its signature from one infected machine.
For tech support communities cleaning multiple systems hit by the same malware family, this signature extraction turns one cleaned system into protection for the rest. Find an unknown threat on machine A, extract its signature, scan machines B through F with the updated local database, find and remove the same threat across all of them. The workflow is genuinely powerful for users handling outbreak scenarios where commercial AV hasn’t caught up yet.
The signatures stay local to the application’s database rather than being shared with any vendor cloud, which fits the manual-control philosophy of the rest of the tool. If you want to share extracted signatures with the broader community, you do that explicitly through the security forums where uVS users congregate, not automatically through telemetry the application itself sends.
Rootkit detection through file and signature checks
Rootkit detection works through two complementary methods. The file check examines what’s actually on disk versus what the operating system is reporting, comparing the system’s file listings against direct disk reads to identify discrepancies that indicate file hiding. Rootkits that intercept system calls to hide their files show up as anomalies between what Windows reports and what’s actually present.
The signature check applies the application’s pattern database against running components, identifying known rootkit families regardless of how well they’ve hidden themselves at the operating system level.
The combination of these two approaches catches both unknown rootkits (through the discrepancy detection) and known ones (through signature matching), providing more comprehensive coverage than either method alone.
Compared to dedicated rootkit scanners like RootkitRevealer (which focuses purely on detection without removal), Universal Virus Sniffer provides both detection and the cleanup mechanisms to remove what’s found.
The script-based removal system handles even rootkits that prevent normal file deletion, generating cleanup operations that execute during system boot before the malicious code loads.
Script-based removal that actually works on stubborn threats
Rather than removing items immediately when you mark them as malicious, the application generates a cleanup script that executes during system restart. This timing matters substantially for stubborn malware. Active malicious processes typically protect their own files from deletion through various mechanisms: file locks, watcher processes that recreate deleted files, kernel-level protection that blocks user-mode delete operations.
By generating the cleanup as a script that runs during the boot process (before the malware loads), the application bypasses all the protection mechanisms that would normally prevent removal. Files get deleted before the processes that would protect them have a chance to start. Registry entries get cleaned before the watchers that would recreate them are loaded. Scheduled tasks get removed before the task scheduler starts processing them.
The script generation is transparent: you can review the script before it executes, modify it if needed, and understand exactly what’s being changed before committing to the cleanup. For technicians who want to document their work or who need to explain to clients what was done, this transparency provides the audit trail that automated tools don’t offer.
The complete system inventory
Beyond the detection-and-cleanup workflow, the application provides what amounts to a complete forensic snapshot of the system. The main view lists every active executable, including processes, services, drivers, autorun entries, scheduled tasks, browser extensions, and various other categories where malware typically hides. Each item shows its full path, command-line arguments, parent process, digital signature status, MD5 and SHA-256 hashes, file size, and creation timestamps.
Filtering options let you narrow the view to specific categories: unsigned executables, recently-created files, files in suspicious locations, files matching specific signature patterns. For investigators trying to understand what’s happening on an infected system, the filtering produces focused views of exactly the categories most likely to contain threats, rather than overwhelming you with the entire system listing at once.
The hash information matters for reputation checking against external services. Copy the SHA-256 hash of a suspicious file, paste it into VirusTotal or similar reputation services, and check whether other security vendors recognize the file.
The application doesn’t perform these external checks automatically (which would require sending data to third parties), but provides the hashes you need to perform the checks yourself when you choose to.
Online signature database and remote scanning
The application connects to an online signature database maintained by the developer community, expanding the local detection capabilities with continuously-updated patterns for known threats. The connection is optional and can be disabled for users who want fully offline operation, with the trade-off being older signature data that doesn’t include the most recent additions.
Remote scanning support lets a technician analyze a system without being physically present. Running on a target machine, the application can generate analysis reports that get reviewed by remote specialists, who then provide cleanup scripts the local user runs.
This workflow is common in security forums where volunteers help users clean infected systems they’re seeing for the first time, with the analysis happening through forum-based back-and-forth rather than direct remote access.
The reporting format is structured enough that experienced uVS users can read the output of a scan they didn’t run themselves and identify suspicious components, which matters substantially for the tool’s role in security forum culture. Users post their scan reports, specialists analyze them, and cleanup scripts come back through the same forum threads.
The Russian-language origin and its practical implications
The application was developed by Dmitriy Kuznetzoff and originated in Russian-speaking security communities, with the original interface and documentation in Russian. English-language interface translations exist and are maintained, but the most active user community remains Russian-speaking.
Security forums in Russian (specifically virusinfo.info and similar sites) are where the most experienced uVS specialists work, with western forums like Wilders Security and MalwareTips having smaller but still active uVS communities.
This origin produces some practical implications for English-speaking users. Documentation in English exists but isn’t always as thorough as the Russian original. Forum support in English communities works but the deepest expertise lives in Russian-language threads that require translation. Some tutorial videos and walkthroughs are originally Russian with English subtitles.
For users willing to navigate this language situation, the depth of expertise available is substantial. For users who specifically want polished English-language documentation and support, the experience is rougher than what commercial security tools provide.
False positive flagging by some commercial AV
A meaningful real-world consideration is that some commercial antivirus products occasionally flag the application itself as suspicious. ESET specifically detected uVS components in early 2023 through their AMS (Advanced Memory Scanner) heuristics, with the detection categorizing the tool as a hacking utility rather than legitimate security software. The detection was eventually addressed, but similar flagging incidents have happened with other commercial AV products across the years.
The reason isn’t that the application contains malicious code; it’s that the techniques uVS uses for forensic analysis (direct memory access, kernel-level inspection, signature extraction) overlap with techniques some malware uses for similar purposes. Commercial AV heuristics that flag suspicious behavior patterns sometimes can’t distinguish between security tools doing legitimate analysis and malware doing the same operations for malicious purposes.
For users running this software alongside commercial antivirus, occasional false positive interruptions are part of the experience. Whitelist exceptions in your AV product handle the issue when it occurs, with the trade-off being you have to trust the application enough to whitelist it explicitly.
Comparison with the alternative tools
The closest comparisons are tools that occupy adjacent niches in the manual malware analysis space. Process Hacker provides similar process and driver inspection with better integration into modern systems but less specific anti-malware tooling. Autoruns from Sysinternals shows autorun entries comprehensively but doesn’t include signature databases or scanning capabilities. Malwarebytes Anti-Rootkit specifically targets rootkit detection but with automated rather than manual workflows.
Universal Virus Sniffer combines elements of several of these tools (the inventory and inspection capabilities of Process Hacker and Autoruns, the rootkit-specific detection of MBAR, the signature extraction unique to itself) into a single workflow oriented toward manual analysis. The result is more powerful than any individual alternative for users who want the manual approach, less convenient than any of them for users who want automated cleanup.
For tech support communities specifically, the workflow integration is the substantial advantage. Forum-based malware removal threads have evolved around uVS reports as the standard format, with specialists trained to read uVS output and produce cleanup scripts within the same workflow.
Tools that don’t fit this established pattern face the friction of changing how forums operate, which is why uVS has remained dominant in its specific niche even as alternatives with different design philosophies have emerged.
Considerations and limitations
The learning curve is genuinely substantial. Users who treat security software as something that just runs and protects them will find this application overwhelming. Understanding what to look for in a system inventory, distinguishing legitimate-but-unusual components from genuinely suspicious ones, recognizing common rootkit patterns, and producing safe cleanup scripts all require knowledge that takes time to develop.
The application doesn’t provide protection in any preventive sense. There’s no real-time monitoring, no scheduled background scanning, no automatic blocking of new threats. The use case is entirely reactive: you suspect a system is infected, you run the application to investigate, you remove what you find. For ongoing protection, conventional antivirus remains necessary alongside whatever forensic work this tool handles.
False positive risk during cleanup is real. Marking a legitimate system component as malicious and including it in a cleanup script can damage system functionality, occasionally to the point of making the system unbootable. The transparency of script review mitigates this, but users without enough knowledge to recognize when they’re about to break something can still produce damaging cleanup operations through mistakes.
The interface, while functional for its purpose, reflects the development environment of an enthusiast project rather than commercial software. New users coming from polished commercial security tools find the interface dense, the terminology unfamiliar, and the visual design utilitarian. The depth that experienced users appreciate is the same depth that intimidates beginners.
Conclusion
For users whose security work involves analyzing infected systems rather than just running protection on healthy ones, Universal Virus Sniffer provides forensic capabilities that mainstream antivirus simply doesn’t offer. The combination of complete system inventory, active signature extraction, rootkit detection through multiple methods, and script-based cleanup that bypasses malware protection covers the practical needs of tech support specialists, security forum volunteers, and advanced users handling difficult infections.
It isn’t software for users who want their security to “just work” automatically. The learning curve is real, the manual analysis requirements substantial, and the responsibility for cleanup decisions falls entirely on the user rather than on the tool’s automated logic.
For its actual target audience (people who treat malware cleanup as forensic work and want the depth that comes with that approach) the tool covers ground that no commercial alternative matches, with a community of specialists who’ve built workflows around it across years of refinement. For everyone else, conventional antivirus and tools like Malwarebytes Anti-Rootkit serve broader needs more comfortably.
Pros & Cons
- Manual malware analysis for situations where automated tools fail or miss threats
- Portable executable with no installation or permanent system footprint
- Active virus signature extraction adds unknown threats to local detection database
- Rootkit detection through both file checks and signature matching
- Script-based cleanup runs during boot, bypassing malware self-protection
- Complete system inventory with full forensic details for every active component
- Used by tech support communities and security forum specialists worldwide
- Transparent operations let you review every change before it executes
- Substantial learning curve oriented toward advanced users and specialists
- No real-time protection or preventive monitoring
- Documentation is more thorough in Russian than in English
- Some commercial AV products occasionally flag the application as suspicious
- False positive risk during manual cleanup can damage system functionality
- Interface design feels utilitarian rather than polished
- Not a replacement for conventional antivirus protection
Frequently asked questions
This software is a portable forensic security tool designed for manual malware analysis and removal. It provides a complete inventory of every active executable, driver, service, autorun entry, and scheduled task on a system, along with signature-based threat detection, rootkit identification, and a script-based cleanup mechanism that bypasses malware self-protection. The target audience is technically deliberate: tech support professionals, security forum specialists, and advanced users handling infections that conventional antivirus can't resolve.
The application scans the system to produce a forensic inventory of every active component, with full details on each item (file path, signature status, hashes, command-line arguments, parent processes). You analyze the output to identify suspicious components, mark them for removal, and the application generates a cleanup script that executes during the next system restart. The boot-time execution bypasses malware protection mechanisms that would normally prevent file deletion or registry modification.
No. The application provides reactive forensic analysis and cleanup rather than ongoing protection. There's no real-time monitoring, scheduled scanning, or preventive blocking. Conventional antivirus remains necessary for ongoing protection, with this tool used alongside it for specific scenarios where automated tools have failed or where deeper manual analysis is needed.
Rootkit detection uses two complementary methods. The file check compares the operating system's file listings against direct disk reads to identify discrepancies that indicate file hiding (a rootkit hiding its files shows up as files present on disk but invisible to normal system queries). The signature check applies the local pattern database against running components, identifying known rootkit families regardless of hiding techniques.
When the application detects a suspicious component during a scan, it can extract the byte signature of the file directly and add it to a local detection database. This turns one infected system into a detection source for similar threats on other systems, since the extracted signature matches the same malware family on any future scan. For tech support communities cleaning multiple systems hit by the same malware variant, this capability accelerates cleanup substantially.
The forensic techniques the application uses (direct memory access, kernel-level inspection, signature extraction) overlap with techniques some malware uses for similar purposes. Commercial AV heuristics occasionally can't distinguish between legitimate security tools and malware doing similar operations, producing false positive detections. Adding the application to your antivirus whitelist resolves the issue, with the trade-off being you have to trust the tool enough to make that explicit exception.
Basic operation (running scans, viewing the system inventory) doesn't require programming knowledge. The cleanup script generation produces scripts automatically based on what you mark for removal, and the syntax is structured enough that reading scripts to understand what they do doesn't require deep technical skills. However, knowing what to mark as suspicious in the first place requires substantial security knowledge, which is the actual barrier to entry rather than programming specifically.
Malwarebytes Anti-Rootkit specifically targets rootkit detection through automated workflows, with cleanup happening through the application's own decision-making rather than user analysis. Universal Virus Sniffer provides broader system inspection beyond just rootkits, with manual analysis as the central workflow rather than automation. For users who want one-click rootkit cleanup, MBAR is more appropriate. For users who want forensic depth and manual control, this tool covers more ground despite the steeper learning curve.

 (3 votes, average: 4.33 out of 5)
(3 votes, average: 4.33 out of 5)